You have probably heard of “Web3 identity” more than a few times within the last few years. Maybe someone was discussing it at work; you saw the term when scrolling Twitter or at dinner when a friend was impressed by Dogecoin taking SpaceX to the Moon. Regardless of what the source was, Web3 is definitely gaining popularity.
However, it is vital to understand that digital identity in Web3 is still in its infancy. Therefore, it’s rapidly evolving, and experts believe that the industry will continue to evolve for quite a several years. Even though the impact and ultimate form of Web3 won’t be able to evolve fully anytime soon, we do have a clear understanding of its working principles and foundation elements.
The Web3 industry has experienced growth over the last few years. Non-fungible tokens (NFTs), decentralized finance (DeFi), and decentralized autonomous organizations (DAOs), to name a few, received immense interest from both media and investors.
As a result, the meaning of Web3 identity also grows, as it works as a fundamental element for Web3 development and as a key driver for realizing the full potential of decentralization. This article will dive into What is Web 3.0 and Web3 digital identity, its uses, pros, cons, and the future.
Key Statistics
 $1.13 billion
$1.13 billion
The market share of Decentralized Identity at the beginning of 2024 amounted to $1.13 billion.
 88.7% CAGR
88.7% CAGR
The Decentralized Identity market is projected to grow at a CAGR of 88.7% by 2027.
 $101.65 Billion
$101.65 Billion
By the year 2030, the market share of Decentralized Identity is expected to grow to $101.65 Billion.
What is Web3 Identity?

In Web2 (the previous version of Web3), a person’s identity varies. One identity can be used to sign into Google, while another can be used to sign into Facebook and more options. Even if the same person uses the same email address for all services, they will still require the user to create separate accounts using separate login credentials.
With Web2, users give access to personal data in exchange for using its platform. This platform will then send your data and own it in a sense. In contrast, Web3 provides a completely different experience, allowing users to have a single identity that’s tied to their digital wallet.
Instead of setting up a separate account on every service, Web3 lets users connect their digital wallet to an application or platform. And the connection is exactly what allows users to decide what data to share. Therefore, users do not need to subject themselves to hundreds of emails clogging their inboxes simply because they signed in to a specific platform. Web3 also allows users to decide whether they want to give the business access to their email when connecting the digital wallet.
To put it simply, the goal of decentralized identity is to give people official proof of identity and also allow them to control their identities in a secure and user-friendly way. Verifiable proof of identity is also required by some services and platforms, like healthcare, banking, and education.
How Does Web3 Identity Work?
Blockchain technology is the foundation of Web3 dApps. Public or permissioned blockchains store identity data, and each individual is assigned a unique Decentralized Identifier (DID) on the blockchain.
DIDs are unique, cryptographically secure identifiers linked to individuals or entities. They are self-managed and not tied to a centralized registry. Blockchain technology and cryptographic techniques guarantee the security and integrity of identity data.
Data on the blockchain is tamper-resistant, and cryptographic signatures provide authentication. A key feature of Web3 identity is decentralization and operation without a central authority. So, the blockchain suits this purpose well because of its decentralized nature.
Web3 identity solutions aim to work seamlessly across different platforms and services, ensuring a user’s DID and credentials are universally recognized. Individuals use digital wallets or identity agents to manage their DIDs, credentials, and interactions with others.
Web3 identity enables individuals to share only the necessary information in specific situations without revealing extra personal data. Web3 identity prioritizes privacy and data minimization. Instead of sharing complete identity documents, individuals provide selective proofs to meet verification requirements.
Decentralized, user-controlled, and blockchain-based identity systems characterize identity verification. Web3 identity verification aims to establish the legitimacy of individuals or entities without relying on centralized authorities, such as governments or traditional identity providers.
Contact Our Web3 Experts
Decentralized Identity
A Decentralized Identity (DID) is a unique digital identifier associated with an individual, organization, or entity. DIDs provide control and ownership of identity-related information to the user in the field of web3 in banking, reduce reliance on centralized authorities, and enhance privacy and security in Web3 digital identity interactions. This is achieved by allowing users to manage their identity information without intermediaries.
Main Characteristics
A DID is a globally unique and persistent identifier represented as a long string of characters. Anyone can create it; no central authority or registry assigns or manages DIDs.
DIDs are commonly associated with blockchain technology or distributed ledgers. A public or permissioned blockchain is the infrastructure for managing and resolving DIDs. The blockchain records the association between the DID and the entity it represents.
DIDs are associated with a pair of public and private cryptographic keys. The public key is openly shared and used for verification, while the DID owner securely keeps the private key.
Each DID has associated metadata known as a DID document. The DID document contains information such as public keys, service endpoints, and authentication mechanisms. It specifies how the DID owner can be authenticated and contacted.
DIDs can be used to request and issue verifiable credentials. Verifiable credentials are digitally signed statements that attest to specific claims or attributes about an individual. These claims can include educational qualifications, age, or membership in an organization.
Users can use their DID and associated credentials to authenticate or share specific attributes, such as a website or service, with a relying party. This allows for authentication without revealing unnecessary personal information.
DIDs enable selective disclosure, allowing individuals to choose which information to share in different contexts. They offer precise control over personal data, enhancing privacy.
DIDs are interoperable across various platforms, services, and applications, following open standards like those defined by the World Wide Web Consortium (W3C), ensuring compatibility.
DIDs improve privacy and security by reducing the need to share sensitive personal information for verification. Cryptographic keys and secure communication protocols ensure data integrity and confidentiality.
Our software engineers are available to provide detailed consultation on data protection in Web3.
Get in TouchComponents of Digital Identity in Web3
-
Decentralized Identifiers (DIDs)
Decentralized Identifiers, commonly known as DIDs, are unique and self-sovereign identifiers. They grant individuals and entities complete control over their digital identities in a decentralized manner. Unlike traditional identities tied to central authorities, DIDs are independently managed.
DIDs are typically represented by a unique string, such as a Universally Unique Identifier (UUID). Each DID is associated with a DID document, which contains critical metadata. This metadata includes public keys for cryptographic verification, service endpoints for communication, and authentication mechanisms.
In the context of Web3, DIDs are often integrated with blockchain technology or distributed ledgers. This integration ensures that DIDs are immutable and persistently associated with their respective DID documents. The blockchain serves as a decentralized registry for recording and maintaining DIDs.
Each DID is equipped with cryptographic keys—an associated public key for verification and a private key for transaction signing. Securely stored by the DID owner, the private key is pivotal in ensuring data integrity and enabling secure authentication.
-
Verifiable Credentials (VCs)
Verifiable Credentials, denoted as VCs, are cryptographic attestations that verify specific claims or attributes about individuals or entities. They offer a secure mechanism for sharing and verifying information without divulging unnecessary personal details.
VCs consist of digitally signed statements that assert particular claims. These statements are signed by trusted issuers, such as universities verifying degrees. This cryptographic signing ensures the credibility and authenticity of the credential.
The applications of VCs are diverse, ranging from educational qualifications and professional certifications to age verification and more. Individuals can present VCs when required, offering a selective disclosure mechanism. This selective sharing minimizes data exposure, strengthening privacy protection.
-
Blockchain
Blockchain technology, or distributed ledgers, is foundational to Web3’s digital identity. It provides a decentralized and tamper-resistant infrastructure for the recording and managing of DIDs and associated identity-related data.
In a technical sense, blockchains establish a decentralized registry of DIDs and documents. Each block in the blockchain ledger contains records of new DIDs, updates to DID documents, and other identity-related transactions.
Decentralization is a hallmark of blockchain networks. This decentralized nature safeguards against single points of failure and censorship, ensuring the reliability and availability of DIDs and related data.
Security in the blockchain is maintained through cryptographic hashing and consensus mechanisms. Any changes to DIDs or their associated documents necessitate consensus among network participants, guaranteeing data security and integrity.
Enhance security and transparency with blockchain to maximize your company’s performance.
Contact usIssues With Digital Identity
User Experience
Since digitalization and Web3 identity puts users at the center of a company’s business operations and decisions, they have to get a seamless user experience. However, it seems to have become a great challenge for all digital applications. Developers should focus on the customer journey while also making sure they launch customer-centric solutions. Finding the perfect balance between user security, usability and convenience may become one of the most significant challenges for digital ID solution providers.
Scale and Coverage
Since digital identity can be a hassle and does not guarantee security, one of the main challenges of Web3 identity will be persuading users to adopt digital ID solutions. And this also adds another layer of complexity for development companies since they should make the process as smooth as possible, ensuring the protection of user data. Remember that users avoid unproven systems, which may prevent your product from further development.
Monetization
Developers should monetize their software solutions which require users to go through digital identity by asking to pay additional fees for digital ID applications. Even though there is a growing number of cases where users are willing to pay, mainly in developed European countries, the volume is still small, and there is no guarantee it will grow in the future.
Self-Sovereign Identity in Web 3.0

Digital identity, mainly self-sovereign identity (also known as SSI), is key to enabling Web 3.0 since it is all about decentralization and data privacy. While Web 2.0 is characterized by careless data sharing and its uncontrollable use for commercial purposes, Web 3.0 changes that paradigm giving users control over their data.
Self-sovereign identity (SSI) is considered to be the most efficient way of digital identity for Web 3.0. SSI refers to the method of identity that centers on the control of user data. Enabling Web3, SSI eliminates the need to store personal data entirely on a central database and allows users greater control over what information they share while protecting their privacy. Being a fully user-centric and user-controlled approach to exchange digitally signed information, SSI is believed to be also the most secure way for digital identity in Web3.
As the name suggests, SSI technology allows users to self-manage their digital identities without the need for third-party providers to store and manage the information. The three main plates in the SSI system are:
- Holder: The individual creates a decentralized identifier using a digital wallet app and receives Verifiable Credentials.
- Issuer: Party with authority to issue Verifiable Credentials.
- Verifier: Party checking the credential.
To stay efficient and secure, SSI technology works following these key principles:
- Existence: Users should be able to exist in the digital world without relying on a third party.
- Control: Users should get the entire authority over their digital identities and the information they share.
- Access: Users must always have seamless access to their personal information.
- Portability: Users must have an opportunity to easily bring their identities and credentials anywhere and share their data from one platform to another.
- Interoperability: Identities should be used as widely as possible by various systems.
- Consent: Users must give permission for an entity to use or access their data.
- Minimization: A digital identity solution must allow users to share the least possible amount of information that another party needs to minimize the risk of stealing sensitive personal data.
- Protection: Users’ rights to privacy must always be protected, and safeguards should exist against tampering and monitoring information. In addition, data traffic must also be encrypted end-to-end.
Benefits of Decentralized Identity

Your Identity is Hard to Verify
Using traditional login methods, users should remember the right credentials to access an account. That means anyone who knows your credentials can access your personal data pretending to be you. In contrast, decentralized identity verification requires physical access to the user’s device to make sure that the needed user enters an account, which is a much higher barrier for any hacker.
A Lower Risk of Mishandled Data
It isn’t a surprise that cybercrime is on the rise today. And recent data breaches of large companies like Facebook have called for a debate about the security of third-party data storage. When companies aren’t able to protect user data, they not only risk losing customers’ loyalty but also leave numerous users vulnerable to identity theft and cyber-attacks. That is why decentralized identity allows users to control their own data, making it harder for attackers to access it and, therefore, reducing the risk that user data will be compromised.
Transactions are Set in Stone
If previously attested information is altered, it gives many opportunities for hackers. By decentralizing transaction information thanks to blockchain signatures, altering verified information is almost impossible. Since all transactions happening on the blockchain are immutable, it ultimately prevents anomalies in the network and guarantees that verified data had not been tampered with.
Convenience
Modern people seek extra convenience in everything they do. Since almost everything from ordering food to checking with a doctor happens through software, digital spheres should always be convenient and user-friendly. Using traditional methods, it takes a long time to access the service as you need to register online, set your password, and choose security questions that will further prove your identity. That is why decentralized identity eases the sign-up and sign-in process, allowing users to enjoy their favorite services with no hassle. They will need to create an identity once and then reuse that verified identity over and over again.
Use cases of SSI in Web 3.0
Since SSI is known for convenience and efficiency, its uses are growing with the development of new technologies and spheres. Let’s explore the most common ones below:
-
DeFi, CeDeFi in Web3
Identity verification in Web3 is essential in both DeFi and CeDeFi. As a result, SSI develops an excellent identity layer, working as a bridge between traditional data-heavy interactions and an anonymous DeFi approach. In addition, CeDeFI offers the financial infrastructure for SSI adoption.
Explore Smart contract development services

Setting standards in the industry, we develop craft fail-proof smart contracts for businesses across sectors and help startups fill their expertise gaps
-
NFTs in Web3
In an NFT market, SSI is used to verify the blockchain identity of creators, owners, and buyers of tokens across their entire lifecycle. Regardless of the blockchain ledger NFTs are hosted on, SSI has been shown to solve the provenance issue. The key thing about SSI is that it also allows for the consumption of media/content directly from the creator without the need for a distribution channel, allowing for decentralized content consumption a reality.
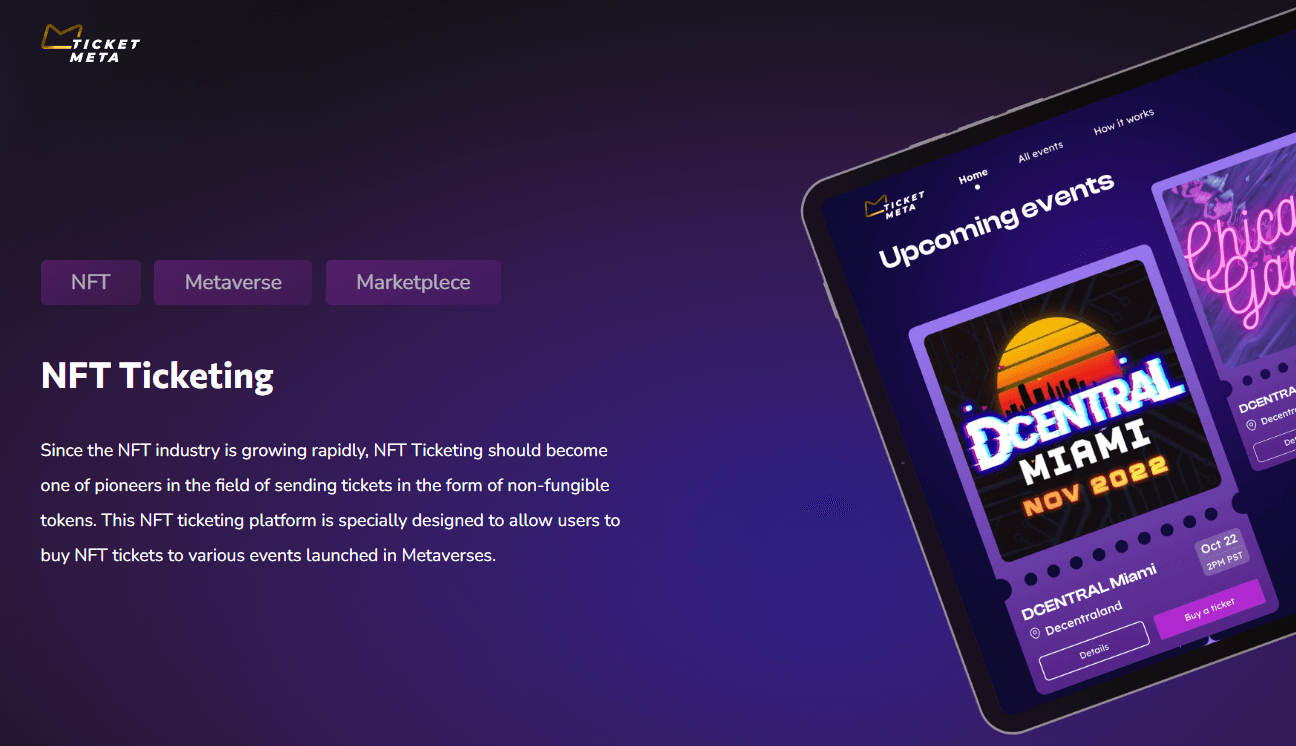
NFT Ticketing
The NFT Ticketing platform is a project designed for the issuance and management of event tickets as non-fungible tokens (NFTs). This platform is aimed at being a pioneer in the NFT ticketing space, particularly for events in Metaverses.
-
Gaming in Web3
Even though it is one of the newest use cases of SSI, NFT and SSI working together brings a whole new gaming experience. While NFTs are great for bringing uniqueness and user satisfaction, SSI is an excellent choice for storing and updating characteristics.

Gamifly
Gamifly is a Web3 platform designed to integrate traditional gaming companies with the Web3 ecosystem. It provides an easy-to-use SDK for onboarding games onto the blockchain and offers a seamless user experience for earning and transferring tokens within various games.
-
Metaverse in Web3
Finally, SSI seems to benefit Metaverse as well. Verified and interoperable information will be essential in the Metaverse. This is used on many levels starting from original identity verification when users create a profile and ending with countless transactions within the virtual world.
Check Our Case MetaMine

MetaMine is a digital asset platform designed for the Metaverse, focusing on AR and VR technologies. It allows users to create digital copies of real-life items (like clothes, jewelry, cars, houses) and use them in various Metaverse environments.
Identity verification in Web3 is essential in both DeFi and CeDeFi. As a result, SSI develops an excellent identity layer, working as a bridge between traditional data-heavy interactions and an anonymous DeFi approach. In addition, CeDeFI offers the financial infrastructure for SSI adoption.
Explore Smart contract development services

Setting standards in the industry, we develop craft fail-proof smart contracts for businesses across sectors and help startups fill their expertise gaps
The Future of Decentralized Identity
With the increased use of NFTs, crypto, and the growing popularity of Metaverse and Web3, the future of internet identity will be decentralized. That is because it provides higher security, gives users control over their data, boosts efficiency, and provides simplicity in using services. This entirely new approach seems to dramatically change how users interact with services, how transactions are made, authenticated and how data is managed.

How Can Interexy Help?
Interexy is a trusted app & web development company focusing on blockchain development services. As an expert in the blockchain and NFT ecosystem, we use the latest technologies and check market trends, offering our clients innovative, secure, and stable products.
We have a well-thought-out hiring process, which allows us to collect the best talents from all across the world. Therefore, each client gets a dedicated team of blockchain experts who know every aspect of the industry and deliver top-notch quality solutions for business growth.
If you have a question or want to share your project idea, our team will be happy to assist.
Book a CallFinal Thoughts
Decentralization, transparency, security, and efficiency are pervading characteristics of Web3. Therefore, users also want to reap the benefits of the new version of the internet. And digital identity allows users to get control over their data.

FAQs
-
What is Web3 Identity?
Web3 identity allows users to connect their wallets to a specific network. After the first authentication, users are allowed to use the same identity for all services they use.
-
How does Decentralized Identity Work?
Decentralized identity, also known as self sovereign identity, is an open-standards-based identity framework that utilizes digital identifiers and verifiable credentials that are self-owned, safe, independent and allow for trusted data exchange.
-
What are the benefits of self-sovereign-identity (SSI)?
SSI allows users to control their own data, how it is used by services, and how it will be managed further. In addition, SSI boosts security and simplicity.